Systems that don't flinch under real pressure.
Security that holds steady
as systems evolve.
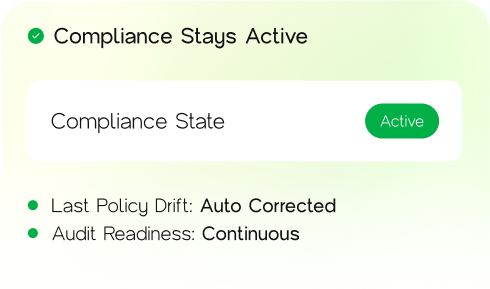
Built into operations — so trust, control, and compliance don't depend on last-minute fixes.



Outwork restores security at the operational layer
where systems change every day, not once a year.

Outwork's Approach
We treat security as part of how systems run — not something layered on later.
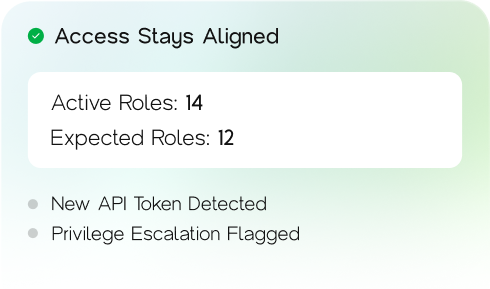
How access is granted and reviewed
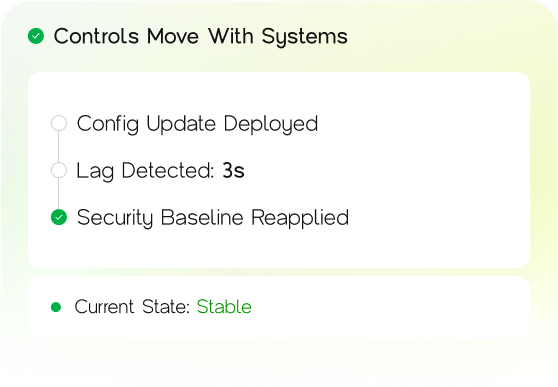
How changes are monitored over time
How evidence is produced without disruption
Capabilities
Role-based access design
Access structured around responsibility, not convenience or legacy permissions.
Ongoing access review and hygiene
Permissions kept current as teams, roles, and systems change — without disruption.
Infrastructure and system-level monitoring
Security visibility embedded into live systems, not separated from operations.
Detection of abnormal behaviour
Unusual patterns identified early, before they turn into incidents or audits
Outcomes
Systems teams spend less time proving, more time operating
Clearer ownership of access and controls
Predictable audit cycles
Reduced operational friction around compliance
Fewer security surprises
Where This Fits Best
This model works best for organizations that...
Operate in regulated or high-risk environments
Face recurring audits and compliance reviews

Manage sensitive data and critical systems

Need security that scales with operations

Contact Us
Partner with OutworkTech – where intelligence becomes advantage.